You can lock down your application code and still get burned by what ships around it: the base image you inherited three years ago, the Dockerfile that quietly runs everything as root, or the Terraform change that made a storage bucket public.
That’s why we built two new scanners that run alongside the rest of Corgea: Container & Image Scanning and Infrastructure as Code (IaC) Scanning.
The pain we’re solving
Most teams don’t intentionally ship risky infrastructure. It happens because:
-
Containers hide a lot of surface area. A simple
FROM python:3.11-slimcan pull in OS packages and libraries with known CVEs. Those vulnerabilities don’t show up in your app dependency files. -
IaC changes are fast and hard to review. Kubernetes, Terraform, Helm, CloudFormation… it’s easy to miss one misconfiguration that opens a door, or one secret that ends up committed forever. Dedicated secrets scanning helps catch the credential side of that problem.
You end up catching issues late, during a deployment review, a production incident, or a “why is this exposed?” message in Slack.
What we built (and why)
We wanted the same thing customers ask us for across AppSec and platform teams:
-
Catch problems before deployment
-
Make findings actionable (not noisy)
-
Cover what developers actually ship: code, dependencies, containers, and infrastructure definitions
So we added two scanners that focus on the “last mile” of modern delivery.
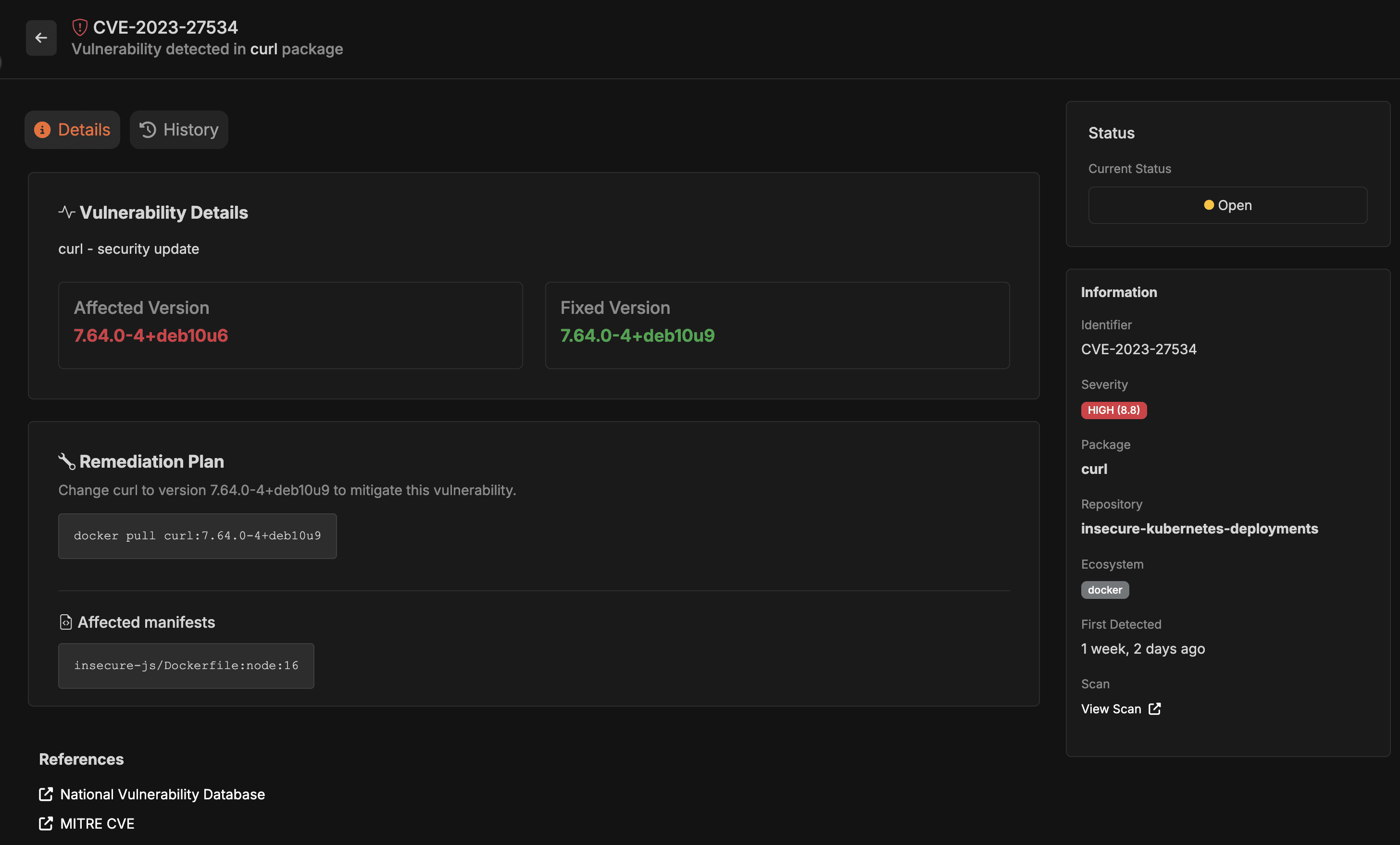
Container & Image Scanning
Corgea now scans container images referenced in your repo to identify known vulnerabilities inside the image layers—including base OS packages, system libraries, and installed software.
-
Corgea discovers images automatically by looking for Dockerfiles and docker-compose files.
-
It extracts the image references (for example
FROM python:3.11-slimorimage: postgres:15) and analyzes them for known issues. -
Supports common registries including Docker Hub, GHCR, GCR, Quay, MCR, Amazon ECR Public, and GitLab Container Registry.
No setup required. If Corgea detects Docker files, container scanning is enabled automatically.
Infrastructure as Code (IaC) Scanning
IaC Scanning finds security misconfigurations and exposed secrets in infrastructure code before it reaches production.
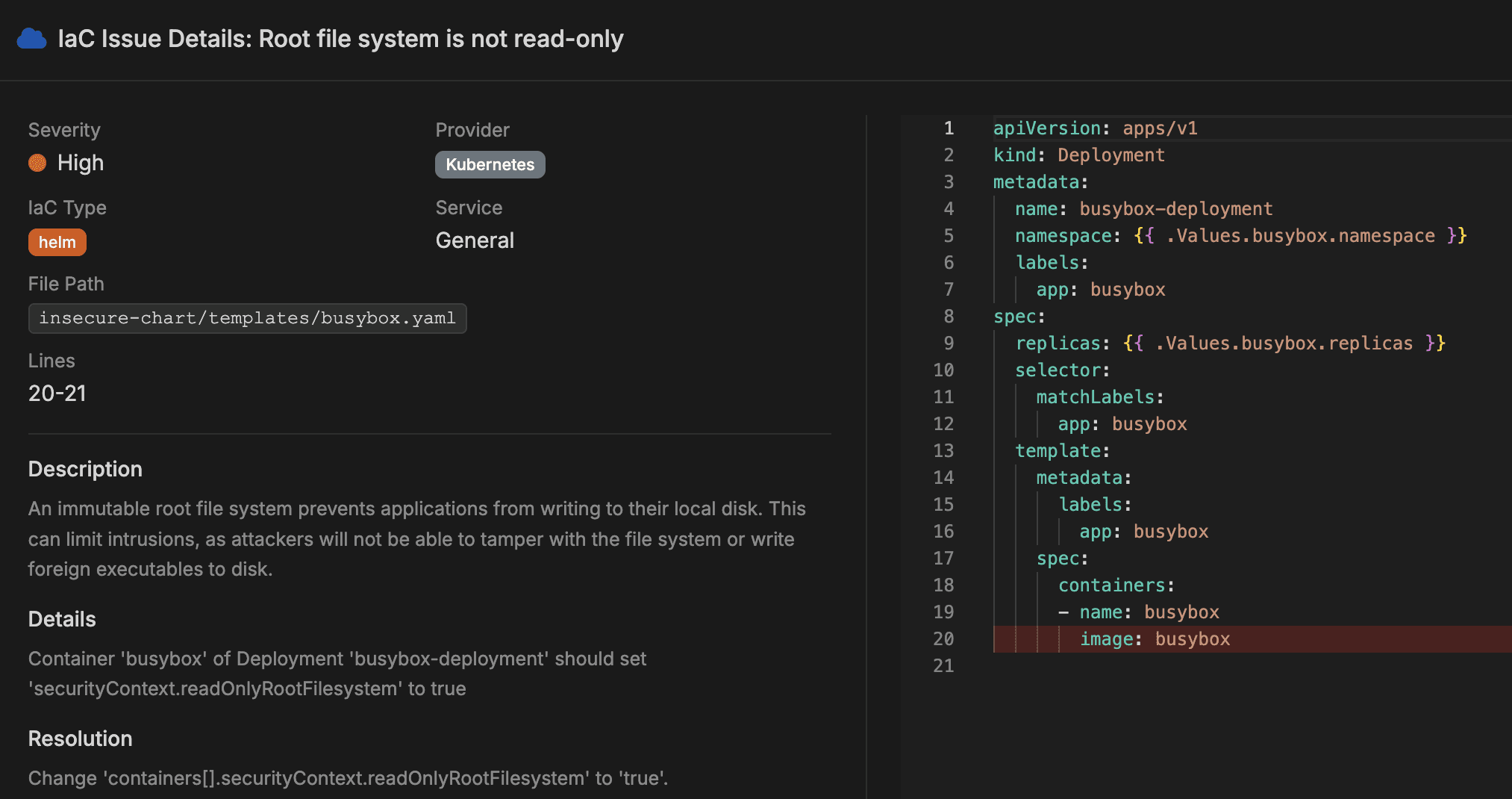
It covers common formats like Kubernetes manifests, Terraform, Dockerfiles, CloudFormation, Azure ARM Templates, and Helm charts, and produces findings with severity and remediation guidance.
Examples from the docs include things like:
-
Kubernetes: privileged containers, missing security context/resource limits, exposed secrets, network policy issues
-
Terraform: public resources, unencrypted storage, overly permissive IAM, missing logging/monitoring
-
CloudFormation / ARM: open security groups, missing encryption/logging/diagnostic settings
Corgea:
-
discovers IaC files,
-
applies checks based on file type,
-
detects misconfigs and secrets,
-
creates trackable issues,
-
produces reports prioritized by severity.
Getting started quickly
Scan what actually reaches production: images and infrastructure definitions, not just application code. Flip it on, run it in CI, and focus your time on the handful of findings that matter.