If you’re evaluating Snyk vs Semgrep, you’re probably balancing two very different approaches to application security. Snyk is a broader developer-first AppSec platform with strong dependency, container, and infrastructure coverage. Semgrep is faster, lighter, and more customizable for teams that want a flexible static analysis engine and tight control over rules. Both are credible tools, and both can fit well depending on how your team works. The real trade-off is that both primarily help you find problems. They do not fundamentally remove the remediation bottleneck. Corgea approaches the problem from a different angle: it can replace point tools like Snyk or Semgrep for teams that want an AI-native platform, and it can also work alongside those tools to auto-generate verified code fixes as pull requests, so teams spend less time triaging and more time actually closing security findings.
TL;DR: Snyk excels at developer-first platform coverage across SCA, containers, IaC, and SAST. Semgrep is strongest in fast, customizable rule-based static analysis with broad language support. Both detect vulnerabilities but leave most remediation work to your developers. Corgea can replace point tools like Snyk or Semgrep for teams that want an AI-native AppSec platform, or work alongside them to detect business logic flaws, find auth issues, and auto-generate verified code fixes as pull requests.
What Is Snyk?
Snyk is a developer-first application security platform built around the idea that security checks should show up where developers already work: in the IDE, in pull requests, in source control, and in CI/CD. The company is best known for software composition analysis, but over time it expanded into SAST with Snyk Code, container image scanning, IaC scanning, and API/web security add-ons. That breadth is one reason Snyk is often shortlisted by engineering-led teams that want a single vendor for multiple AppSec workflows instead of stitching together separate point tools.
For source code, Snyk Code uses an AI-based semantic analysis engine, priority scoring, and data-flow views to help teams understand what matters first. Its developer ergonomics are a major selling point: the platform offers native integrations for GitHub, GitLab, Bitbucket, and Azure Repos, plus IDE plugins and CLI workflows. Snyk also supports deployment models beyond pure SaaS, including Broker for self-hosted SCMs and a local no-upload engine for stricter environments.
Key capabilities include:
- Broad platform coverage across SCA, SAST, container security, and IaC scanning.
- Developer-friendly workflows in IDEs, pull requests, repos, CLI, and CI/CD.
- Priority scoring and data-flow views to help teams triage high-risk findings.
- Automated fix support for some issues through Snyk Agent Fix and automatic dependency Fix PRs.
- Flexible deployment options including SaaS, Broker-connected self-hosted SCM support, and local no-upload scanning for Snyk Code.
Known limitations and trade-offs:
- Pricing can climb quickly as contributor counts rise or teams add more product modules.
- Snyk Code language support is narrower than Semgrep Code’s, even though the broader platform covers many ecosystems.
- Automated code fixes are still bounded by supported languages and currently do not support inter-file fixes.
See our Snyk vs Checkmarx comparison →
What Is Semgrep?
Semgrep started as a lightweight static analysis engine and has grown into a broader AppSec platform centered on Semgrep Code, Semgrep Supply Chain, Semgrep Secrets, and Semgrep Assistant. It is still best known for fast, rule-driven SAST and for giving security engineers unusually fine-grained control over rules and policies. That makes it popular with teams that want a scanner they can tune themselves rather than a heavily abstracted platform that hides the rule logic.
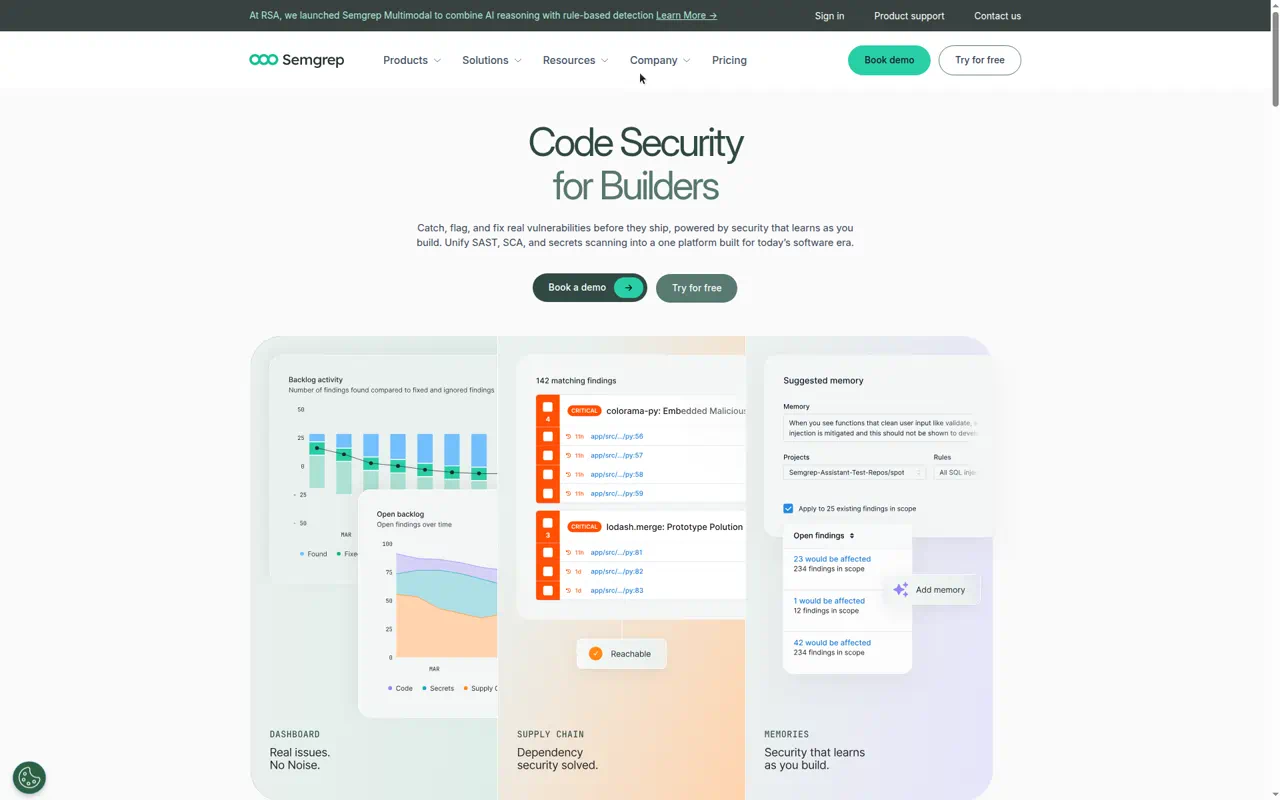
As of 2026, Semgrep Code supports 35+ languages, with strong coverage in mainstream engineering stacks and cross-file analysis for many of its generally available languages. Semgrep Supply Chain adds SCA with reachability for supported ecosystems, and Semgrep Secrets adds semantic secrets detection plus validation to prioritize active credentials. Semgrep Assistant layers AI on top of this workflow with explanations, suggested fixes, auto-triage, and noise filtering. Semgrep can also run in local or CI-driven modes so code does not have to leave your environment, while enterprise customers can add on-prem SCM support, custom CI/CD integrations, and dedicated infrastructure.
Key capabilities include:
- Fast, customizable SAST with YAML-based rules and strong security engineer adoption.
- 35+ language support for Semgrep Code, including cross-file analysis in major languages.
- Native SCA and secrets detection through Semgrep Supply Chain and Semgrep Secrets.
- AI-assisted triage and remediation guidance through Semgrep Assistant / Multimodal.
- Flexible deployment patterns including local scanning, CI-based scanning, and enterprise deployment options.
Known limitations and trade-offs:
- Coverage depends heavily on rule quality and policy tuning, especially for custom use cases.
- It is not a full all-in-one platform in the same way Snyk is for containers, IaC, and adjacent security categories.
- AI remediation is helpful but not the same as closed-loop remediation, so teams still need engineers to review, apply, and operationalize fixes.
What Is Corgea?
Corgea is an AI-native AppSec platform that can replace point tools like Snyk or Semgrep for teams that want one platform for scanning plus remediation, and it can also work alongside existing scanners when teams prefer to keep their current stack. It integrates with Snyk, Semgrep, Checkmarx, GitHub Advanced Security, Coverity, and others, but it also provides native AI SAST, business-logic and auth scanning, dependency scanning, secrets detection, container scanning, IaC scanning, and reachability analysis.
What makes Corgea different is that remediation is the center of the product, not an optional follow-up workflow. Corgea generates verified pull requests for vulnerabilities, validates the proposed fixes, and pushes remediation into the code review process developers already use. That means security teams can use Corgea as their primary AppSec platform, or as the action layer that turns findings from Snyk, Semgrep, and other tools into merged fixes.
In practice, Corgea fits best when you want fewer disconnected scanners, shorter MTTR, and a platform that can move from detection to code change without leaving the developer workflow.
Snyk vs Semgrep vs Corgea: Comparison Table
| Feature | Snyk | Semgrep | Corgea |
|---|---|---|---|
| Primary Focus | Broad developer-first AppSec platform | Fast, customizable code analysis platform | AI-native AppSec platform with auto-remediation |
| SAST | ✅ Snyk Code with semantic AI analysis and IDE workflows | ✅ Semgrep Code with rule-based analysis across 35+ languages | ✅ AI-native SAST - Can detect business logic flaw and auth issues |
| SCA | ✅ Mature SCA / open-source dependency scanning | ✅ Semgrep Supply Chain with reachability for supported ecosystems | ✅ SCA with AI Reachability |
| DAST | ⚠️ Available via Snyk API & Web add-on | ❌ No native DAST | ⚠️ Works with existing DAST findings and workflows rather than replacing DAST tools |
| IaC Scanning | ✅ Native IaC scanning | ⚠️ Limited via Semgrep Code rules for formats like Terraform and Dockerfile | ✅ Native IaC scanning |
| Container Scanning | ✅ Native container security | ❌ No native container image scanning | ✅ Native container/image scanning |
| Secrets Detection | ⚠️ Hardcoded secrets surfaced through code scanning, not a standalone first-party secrets product | ✅ Native secrets detection with validation | ✅ Native secrets detection |
| Auto-Remediation / AI Fix | ⚠️ Agent Fix plus automatic dependency Fix PRs in supported workflows | ⚠️ AI guidance and suggested fixes, with some autofix support | ✅ AI-generated PRs |
| CI/CD Integration | ✅ Strong GitHub, GitLab, Bitbucket, Azure Repos, IDE, CLI, API support | ✅ Strong GitHub, GitLab, Bitbucket, Azure DevOps, IDE, CLI support | ✅ GitHub, GitLab, Bitbucket, Azure DevOps, PR-driven workflows |
| False Positive Handling | ✅ Priority scoring, filtering, data-flow context, fewer-false-positive positioning | ✅ Rule tuning, reachability in Supply Chain, AI noise filtering and auto-triage | ✅ Fixes real issues, deprioritizes noise |
| Pricing Model | Per-contributor; free tier, Team from $25/dev/month, larger plans and add-ons | Per-contributor; free tier, Teams from $30/contributor/month, enterprise custom | Free tier, Growth $39/dev/month, Scale $49/dev/month, Enterprise custom |
| Deployment | SaaS, Broker for self-hosted SCM, local no-upload engine for Snyk Code | Cloud platform, local/CI scanning, enterprise dedicated infrastructure and on-prem SCM support | SaaS with enterprise single-tenant option |
Security Coverage: Snyk vs Semgrep vs Corgea
If your main question in Snyk vs Semgrep is “which one covers more of my attack surface?”, Snyk usually comes out ahead. Snyk is built as a multi-product platform: SCA, SAST, container scanning, IaC scanning, and API/web testing are all part of the commercial conversation. For organizations trying to consolidate vendors, that is attractive. You can cover source code, dependencies, images, and infrastructure from one dashboard, with consistent repo and CI/CD integrations. That breadth is especially valuable for teams that want one procurement path and one platform owner.
The trade-off is that not every Snyk module is equally deep for every team. Snyk Code is solid for mainstream application security use cases, but it is still just one part of a broader platform. If your security program is heavily centered on custom rules, niche frameworks, or very specific policy logic, Snyk may feel more opinionated and less transparent than rule-first tools.
Semgrep is narrower in philosophy, but broader than many people remember. It is no longer just a point SAST engine. Semgrep Code handles static analysis across 35+ languages, Semgrep Supply Chain adds SCA with reachability for supported ecosystems, and Semgrep Secrets adds validation-backed secret scanning. That said, Semgrep still feels like a code-analysis-centric platform. It does not offer native container image scanning, and its IaC story is more rule-oriented than a dedicated IaC product strategy. For some teams that is a limitation; for others it is a feature because it keeps the product simpler and more controllable.
Corgea approaches coverage differently. It offers its own AI-native SAST, dependency scanning, secrets detection, container scanning, and IaC scanning, so it can replace point solutions for teams that want a more consolidated platform. It can also sit on top of the tools you already run. That means you do not have to choose between Snyk breadth and Semgrep flexibility if your real problem is not coverage, but getting findings fixed quickly.
Auto-Remediation: Where Both Tools Fall Short
This is the most important difference in the three-way comparison. Snyk and Semgrep are fundamentally detection-centric platforms. They are designed to identify issues, prioritize them, and surface them in developer workflows. They both now include AI-assisted remediation features, but in practice those features are still support systems for developers, not true closed-loop remediation.
Snyk Agent Fix can generate candidate fixes for supported Snyk Code findings and automatically retest them with Snyk’s code engine. Snyk also supports automatic Fix PRs for dependency upgrades when a new vulnerable package version needs to be bumped. Those are useful capabilities, especially for common cases. But they are still bounded: code autofix language coverage is limited, inter-file fixes are not supported, and teams still need developers to decide when and how to apply the suggestions. For many organizations, that means remediation remains a developer queue-management problem.
Semgrep’s AI layer is similarly helpful without fully closing the loop. Semgrep Multimodal can explain findings, auto-triage likely false positives, suggest fixes, and in some cases help with dependency upgrade guidance and autofix. That improves signal and reduces the time required to understand a finding. But Semgrep is still primarily telling the developer what to do next. The workflow is better, not fundamentally different.
Corgea is built around a different end state: actual code changes submitted as pull requests. Instead of stopping at “here is the issue” or “here is a suggested snippet,” Corgea can be the primary platform producing those findings and fixes, or it can take scanner findings from tools like Snyk and Semgrep and generate verified fixes inside the repo workflow. That is the distinction many teams care about most once they already have enough scanners. Detection creates work. Auto-remediation removes work.
Developer Experience & CI/CD Integration
Snyk’s strongest argument is developer experience. The platform has long been optimized for where developers already live: IDE plugins, PR checks, CLI, SCM-native workflows, and CI/CD integrations. For many teams, Snyk feels easier to roll out than more security-team-centric products because it presents findings in a familiar way and keeps the path from detection to assignment straightforward. If your culture is “shift security left and keep it inside the developer workflow,” Snyk is easy to understand.
Semgrep is also highly developer-friendly, but in a different style. It tends to appeal to teams that want speed, clear rule behavior, and low operational friction. Security engineers like it because they can author and tune YAML rules. Developers like it because scans are fast and the feedback can be made very targeted. Semgrep also supports one-click CI/CD deployment on Semgrep-managed infrastructure and integrates with common SCMs, IDEs, Slack, Jira, and APIs. The main difference is that Semgrep often expects more active policy ownership from the security team.
As of 2026, that difference matters. Snyk often feels like a product you subscribe to and operationalize. Semgrep often feels like a scanner platform you shape over time.
Corgea plugs into the same workflows but changes what appears in them. Instead of just adding more alerts to GitHub, GitLab, Bitbucket, or Azure DevOps, it can submit remediation PRs developers can review like normal code. That is a better fit for teams that already have mature CI/CD and code review habits but do not want AppSec to live as a separate triage stream forever. It also means teams can standardize on Corgea as the main developer-facing platform while still ingesting results from legacy or specialist scanners.
Accuracy & False Positive Rates
False positive handling is one of the hardest parts of any AppSec tooling decision, and it is one reason Snyk vs Semgrep is rarely a simple apples-to-apples choice. Snyk positions Snyk Code as a semantic, AI-based engine that produces fewer false positives than older rule-heavy scanners. Its data-flow views, priority scores, issue filtering, and curated developer guidance all help teams focus on what is most likely to matter. In practice, teams that value packaged signal over tunability often prefer this model.
The downside is that you are trusting Snyk’s analysis model and prioritization framework. If your team wants to know exactly why a rule fired, how it was tuned, or how to customize it deeply across unusual code patterns, the platform can feel less transparent than Semgrep.
Semgrep approaches the problem from the other direction. It gives you rule-level control and now adds AI noise filtering, auto-triage, and explanation layers on top. Semgrep’s strength is that high-signal rulesets can be extremely practical when they are well tuned to your stack. Its weakness is that accuracy is partly a product of how disciplined your rules and policies are. In other words, Semgrep can be excellent, but it often rewards teams that invest in it.
Corgea changes the accuracy conversation by focusing on actionability. Reachability analysis, endpoint-aware context, business-logic and auth detection, and verified fix generation all help reduce the gap between “possible issue” and “issue worth fixing now.” That is not the same thing as saying scanners stop producing noise. It means Corgea helps teams spend less time arguing with the output and more time resolving the findings that survive scrutiny.
Pricing & Total Cost of Ownership
Snyk’s direct pricing is clear enough to understand, but total cost of ownership can still surprise teams. The free tier is attractive for evaluation. Team starts at $25 per contributing developer per month, and larger plans layer in more capabilities, with products often purchased separately and add-ons such as API/web testing changing the economics further. For teams that want a broad AppSec platform, this can still make sense. The risk is that Snyk gets expensive as more developers, repositories, and modules come under management.
Semgrep is similar in that it is priced per contributor, but its packaging feels more modular in a different way. The free edition includes Code and Supply Chain for up to 10 contributors. Teams pricing starts at $30 per contributor per month for Code or Supply Chain, with Secrets priced separately. That can be economical if you want one or two Semgrep products, especially for teams that value its speed and flexibility. It can become less straightforward when you want broad platform coverage plus enterprise deployment flexibility and advanced AI features.
The bigger cost question is not just license price. It is how much engineering and AppSec time the tool consumes after purchase. Tuning rules, triaging noisy findings, filing tickets, and chasing remediation all cost real money.
Corgea’s public pricing is more straightforward than many enterprise AppSec vendors. The Free tier is $0, supports up to 2 team members and 10 repos, and includes AI SAST, logic and auth scanning, dependency scanning, secrets detection, container scanning, and IaC scanning. Growth starts at $39 per developer per month, supports up to 100 repos, and adds PR scanning, code quality, Corgea Agent, JIRA integration, and license enforcement. Scale starts at $49 per developer per month, supports up to 200 repos, and adds custom rules, blocking rules, reporting and analytics, team management, and APIs/webhooks. Enterprise is custom-priced for unlimited scale plus SSO, SCIM, single-tenant deployment, SLA management, audit logs, and premium support.
Corgea matters here because it targets the hidden cost directly. If you already pay for scanners but still carry a months-long fix backlog, your most expensive problem is usually not detection coverage. It is remediation labor. Corgea can replace multiple point tools for some teams, and it can also work alongside Snyk, Semgrep, or both to reduce the manual effort required to turn alerts into merged fixes.
Compliance & Enterprise Readiness
Enterprise buyers usually care about more than scan results. They care about deployment patterns, identity controls, policy enforcement, reporting, and whether a product fits into an existing governance model. Snyk has a mature enterprise story here. Its pricing page and docs emphasize SSO, policy management, reporting, support for self-hosted source control through Broker, regional data residency, and compliance posture such as SOC 2 Type II and ISO certifications. For organizations standardizing on a single commercial AppSec vendor, that matters.
Semgrep’s enterprise posture is different but credible. The Teams and Enterprise tiers add SSO, policy engine capabilities, RBAC, private rules, on-prem source code management support, custom CI/CD integrations, and optional dedicated infrastructure. Semgrep is often appealing in regulated engineering environments because it can run locally or in CI in ways that reduce code movement, while still giving security teams centralized policy and findings management. The platform tends to resonate with organizations that want strong control and deployment flexibility without giving up modern AI-assisted workflows.
For some buyers, the question is not whether Snyk or Semgrep is enterprise-ready. Both are. The question is whether enterprise maturity alone solves the operational bottleneck after alerts are found.
Corgea complements that part of the stack. Its enterprise-oriented offerings include APIs, webhooks, reporting, SLA management, audit logs, and single-tenant deployment in higher tiers. More importantly, it can fit into existing enterprise scanner estates, or replace parts of them, depending on how much consolidation a team wants. That is especially useful in large organizations already running multiple tools for different business units.
Which Tool Should You Choose?
Choose Snyk if you want a broad, developer-first AppSec platform with strong dependency scanning, container coverage, IaC scanning, and polished SCM/IDE integrations. It is a good fit when consolidation matters and your team prefers opinionated workflows over building and curating lots of custom rules.
Choose Semgrep if you want fast static analysis, strong custom rule capabilities, broad language support, and a platform that security engineers can shape over time. It is especially compelling when you care about rule transparency, tuning control, and getting good code analysis coverage without buying into a heavier all-in-one platform.
Choose Corgea if you’re tired of growing vulnerability backlogs and want to go from detection to remediation. Corgea is a fit when you want an AI-native AppSec platform that can replace point tools like Snyk or Semgrep, or when you want to keep your existing scanners and make them actionable by generating verified fixes as pull requests.
Frequently Asked Questions
What is the difference between Snyk and Semgrep?
Snyk is a broader AppSec platform with strong SCA, container, and IaC coverage plus SAST through Snyk Code. Semgrep is more centered on fast, customizable code analysis, though it now also includes Supply Chain and Secrets products. In short: Snyk is usually the broader platform, while Semgrep is usually the more customizable code analysis engine.
Can I use Snyk and Semgrep together?
Yes. Many teams use more than one security tool because no single scanner catches everything equally well. In practice, Snyk and Semgrep can complement each other, especially when one team values Snyk’s broader platform coverage and another values Semgrep’s custom rules and fast feedback loops.
Which is better for SAST: Snyk or Semgrep?
That depends on what you mean by “better.” Snyk is usually better if you want a polished, developer-first SAST workflow inside a broader platform. Semgrep is usually better if you want 35+ language support, flexible custom rules, and more control over exactly how your code is analyzed.
What are the best alternatives to Snyk and Semgrep?
Common alternatives include GitHub Advanced Security, Checkmarx, Veracode, SonarQube, and Corgea. The right alternative depends on whether you need broader platform coverage, lower-noise code analysis, or an auto-remediation layer that works on top of your existing scanners.
Does Corgea replace Snyk or Semgrep?
It can. Corgea can replace point tools like Snyk or Semgrep for teams that want an AI-native platform with scanning plus remediation, and it can also complement those tools by ingesting their findings and generating fixes. Which model makes sense depends on whether you want consolidation, or you want to preserve an existing scanner investment.
How does Corgea’s auto-remediation work?
Corgea analyzes the vulnerable code in context, generates remediation pull requests developers can review and merge, and validates the proposed changes before handing them off. That can happen on findings Corgea identifies itself, or on findings imported from supported scanners, so the result is a real fix workflow instead of a static alert.
Ready to Fix Vulnerabilities, Not Just Find Them?
Corgea integrates with Snyk, Semgrep, and 20+ other security tools to auto-generate verified fixes. Stop triaging. Start fixing.
